Cybersecurity Compliance Management Hub
Online courses for staff
Phishing, hacking, fraud, and emerging AI-related risks are constant threats for businesses of all sizes. Firms struggle to keep sensitive data secure while staying on top of ever-changing cybersecurity compliance requirements. A single lapse can lead to costly breaches, operational disruption, regulatory penalties, and lasting reputational damage.
With increasing cyberattacks and stricter expectations around cybersecurity compliance, relying on basic policies or reactive measures is no longer enough. Organisations need to embed robust cybersecurity practices across all teams, safeguard critical systems and sensitive data, mitigate risks from emerging technologies such as AI, and demonstrate effective threat management in practice.
Our cybersecurity compliance management hub is designed to help organisations minimise cyber risks and reduce cyber threats by equipping teams with the knowledge and tools to boost cybersecurity awareness. With a flexible approach to cybersecurity training, you can choose from ready-made courses that simplify complex topics like device security and AI risk mitigation, or customise learning solutions to suit your company’s unique requirements.
Who's this for?
This training is ideal for organisations looking to strengthen cybersecurity awareness, ensure compliance, and protect business-critical assets across all levels of their workforce.
-
IT and Security team:
Provides in-depth cybersecurity compliance training to help manage threats, implement policies effectively, and safeguard critical systems -
Compliance Leaders, Managers, and Learning & Development (L&D) teams:
Equips leaders with the knowledge to minimise cyber risks in their teams, while helping compliance and L&D teams enforce policies and deliver training programmes to reduce cyber risk across an organisation -
All Employees:
Delivers accessible cybersecurity e-learning courses and practical guidance to recognise threats, follow best practices, and contribute to a secure organisational culture
See similar compliance topics
Data Protection and GDPR
Maintaining data protection standards and managing online security align with cybersecurity
Financial Crime
Financial regulations ensure the secure handling of financial transactions and reporting
Fraud Prevention
Shared focus on protecting sensitive data, managing online risk and detecting malicious activity
Risk Management
Cybersecurity is driven by risk management, with threat identification and mitigation at its core
Reduce cyber risks and protect your business from cyberattacks
95%
Up to 95% of cybersecurity breaches are due to human error, highlighting the importance of training your workforce.*
48%
As per the UK government’s cybersecurity breaches survey, 43% of businesses reported experiencing a cybersecurity breach or attack in 2025.**
**Gov.uk
Skillcast's commitment to understanding our unique needs and tailoring the solution accordingly has been invaluable and remains so as we evolve annually during our declaration process.
Compliance Team,
Leading African Organisation



Spot a Phishing Attempt
Phishing emails are fraudulent attempts by cybercriminals to trick individuals into revealing sensitive information.

Business Email Compromise
Business Email Compromise (BEC) is a targeted cyberattack where criminals impersonate executives or hack accounts to steal money or sensitive information.
Deepfake Awareness
Deepfakes use artificial intelligence to create fake images, audio or videos that can deceive individuals and organisations.

Understanding Information Security
Information security is essential to protect sensitive business and customer data from unauthorised access, breaches and cyber threats.

Common Cyber Threats
Cyber threats such as phishing, malware, ransomware and unsecured networks pose significant risks to businesses.

Zero Trust Cybersecurity
The zero trust cybersecurity model ensures IT systems remain inaccessible by default, requiring strict verification before granting access.

Bring Your Own Device Security
Bring Your Own Device (BYOD) policies offer convenience and flexibility but also introduce cybersecurity risks.

Device Hygiene
Device hygiene is the practice of keeping digital devices secure and free from cyber threats to protect company data and networks.
Malware
Malware is malicious software designed to harm or exploit computer systems, ranging from viruses and ransomware to spyware and botnets.

Ransomware
Ransomware is a type of malware that encrypts files and demands payment for their release, often causing severe financial and operational damage.
Smishing
Smishing is a targeted phishing scam that uses deceptive text messages to gain sensitive information.

Spear Phishing
Spear phishing targets specific individuals with convincing emails designed to deceive them.

Video Conferencing
Video conferencing is a vital business tool, but it also presents security and privacy risks if not used correctly.

Vishing
Vishing is a social engineering attack where cybercriminals use phone calls to trick individuals into revealing sensitive information.
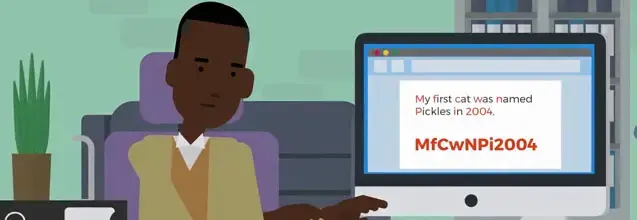
Creating Strong Passwords
Strong password protection is essential to safeguarding company systems from cyber threats such as brute force attacks and password guessing.

Multi-factor Authentication
Multi-factor authentication (MFA) enhances security by requiring users to verify their identity through multiple authentication methods.

Reacting to Password Breaches
Password breaches can lead to unauthorised access, fraud and data theft, often resulting from weak passwords, phishing or insecure networks.

Information Classification
This training helps employees understand different levels of information classification, their restrictions and how to handle data securely.
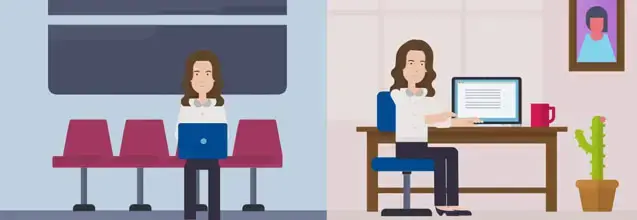
Information Security on the Move
Handling company information securely, especially when working remotely or traveling, is essential to prevent data breaches and security risks.

Tailgating and Piggybacking
Cybersecurity is not just about digital protection but also involves securing physical access to critical systems.

Secure Web Browsing
Practicing safe web browsing helps to reduce security risks and protect sensitive information.
Supply Chain Cybersecurity
A company’s cybersecurity is only as strong as its weakest link and supply chain vulnerabilities can expose businesses to major breaches.

Transferring Information Securely
Securely transferring information is essential to protect sensitive data from breaches, legal risks and business disruptions.
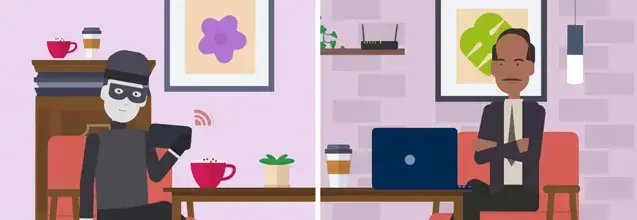
Using Wi-Fi safely
Wi-Fi connectivity offers convenience but also exposes devices and data to security risks if not properly managed.

Advising Customers on Cybersecurity
Cybersecurity is everyone's responsibility, including guiding customers to protect themselves from online threats.

CEO Fraud
CEO fraud is a type of Business Email Compromise where cybercriminals impersonate executives to trick employees into making payments or sharing confidential information.

Guide to Secure Remote Working
Remote work provides flexibility but also introduces cybersecurity risks that can compromise company data and systems.
Think Before You Click
Clicking on malicious links or attachments is one of the most common ways cybercriminals infect IT systems with malware.

Risks in the Use of AI
This training highlights how AI can be used effectively while identifying and addressing potential risks.

Stay audit-ready with a single source of truth
Confidently demonstrate cybersecurity compliance, reduce cyber risk, and save time with everything you need in one place. The Skillcast Compliance Portal gives your organisation a centralised platform to simplify cybersecurity compliance management, track staff knowledge retention, strengthen cybersecurity awareness and monitor adherence to regulations.
Simplify compliance with automated tools
Eliminate the complexity and manual effort of managing cybersecurity compliance across teams. The Skillcast Compliance Portal automates routine tasks, including reminders, follow-ups, and training tracking. This ensures every member of staff completes essential cybersecurity compliance training on time, helping reduce cyber risks and protect your organisation from operational disruption and reputational damage.
Drive engagement and prove compliance
Empower your teams to spot, prevent, and respond to cyber threats with confidence through engaging, high-impact cybersecurity compliance training. From gamified assessments that strengthen real-world threat detection and decision-making to bite-sized cybersecurity e-learning courses that fit seamlessly into busy schedules, this drives stronger knowledge retention and practical ability to reduce cyber risks across your organisation.

Award-winning service
- Have confidence in your compliance programme, supported by a provider trusted by organisations across regulated industries.
- Spend less time resolving issues and more time driving value, with award-winning, responsive support when regulations change or challenges arise.
- Ensure stronger assurance for regulators and stakeholders with a market-recognised, award-winning solution that demonstrates due diligence and quality.
Standard plan:
Ideal for organisations wanting a branded, flexible and fully-managed compliance training platform.
Explore the plan
Recommended
Enhanced plan:
Designed for firms wanting to elevate compliance learning, making it more personal, engaging and efficient.
Explore the plan
Premium plan:
Built for organisations that want a fully integrated, automated compliance platform to simplify compliance at scale.
Explore the plan
Start your compliance e-learning journey with a free trial
With this no-obligation free trial you'll have access to our libraries and compliance platform.
Ready to start? Complete the form, and a member of the Skillcast team will be in touch with further details on how your trial works, what's included, and how to get started.
Feefo Customer Rating ★★★★★ 4.9/5
Where can I track incidents involving personal data?
How can I benchmark my team's cybersecurity awareness?
An anonymous cybersecurity awareness survey can assess your team's understanding of critical security practices. Skillcast offers ready-to-use surveys to benchmark awareness levels and identify areas needing extra focus.
Are Skillcast courses SCORM-compliant?
What other tools are needed beyond training?
Is our training content still compliant with the latest legislation?
- You can check the latest course content updates in our library updates page: https://www.skillcast.com/compliance-course-library-updates
- For major legislative changes, we:
- Send you email alerts to ensure you are notified
- Offer you a free trial of newly created or updated content
- Host webinars with compliance experts to explain the changes and how our training supports your ongoing compliance
Can you translate our content into other languages?
What file types are supported by the Skillcast system?
Features |
Supported file types and details |
|
File Exchange |
File types: PDF, Excel spreadsheets, Word documents, SCORM and xAPI files, and compressed zip files. Max file size: Default is 1GB, can be increased to a max of 2GB |
|
SCORM files |
Versions: SCORM 1.2, SCORM 1.2 for Moodle, SCORM 2004 2nd, 3rd and 4th Edition. Max file size: 1024MB |
|
xAPI file |
Max file size: 2GB |
|
Videos |
File types: MP4 or MOV. Videos must be optimised, with a max file size of 100MB. If the file is bigger, our Design Team can help |
|
Images |
File types: jpg, png and gif. The file size should ideally be 100KB, but it can be up to 250KB |
|
CPD evidence |
File types: Word, PDF, Excel and CSV. File size: the limit should be whatever the portal config option is set to. Servers are set to max 2GB |
|
Policy documents |
PDF or Word File size: the limit should be whatever the portal config option is set to. Servers are set to max 2GB |
|
Offline activities evidence |
File types: PDF, DOC, DOCX, XLS, XLSX, CSV, PNG, GIF, JPEG, JPG, PPTX and MSG. File size: the limit should be whatever the portal config option is set to. Servers are set to max 2GB |
|
Client logo files |
File types provided by client: EPS, PDF, AI and SVG |
|
Registers |
PDF, DOC, DOCX, XLS, XLSX, CSV, PPT, PPTX, POT, PPA, PPS, JPG, JPEG, PJEPG, PNG, BMP, GIF, MP4, MOV, WMV, CPTX, CP, TXT, ZIP and MSG files |
|
Declarations |
JPG, JPEG, PNG, GIF, XLS and XLSX files |





