
Information Security Compliance Training Course
The security of client and internal information is critical for businesses. The consequences of information loss or theft are severe.
The loss or theft of commercially sensitive information may lead to lost revenues, damage to reputation, reduced consumer trust, and even affect a company's survival.
Failure to respect information security may lead to disciplinary measures, fines and even criminal prosecution under various laws.
Our Information Security Training Course helps employees understand information classification, data security, network security, access control to your offices, and prevent information loss or theft.
-
35 Minutes
-
For all staff
-
UK
-
Compliance Essentials Library

What you’ll learn in
this course
- Understand why information security is critical to our business
- Recognise the consequences of data breaches
- Learn how and why information is classified
- Exercise caution when using the internet, emails and other electronic communications
- Comply with Company procedures in relation to network access, portable media and devices, and physical security
- Know how and when to report actual or suspected data breaches
Hear from our customers
Excellent easy-to-use LMS which Skillcast have specifically tailored to our needs to also host a Global Policy Portal and global staff surveys, alongside providing live MI reporting.
Being able to personalise our own training has been a game-changer! Excellent training was provided on how to use the CMS and the support team have been so helpful, patient and quick to reply when I've got stuck.
We have been enjoying e-learning with Skillcast for 10 years now. Their customer service is always at the highest level, always very attentive, responsive, and polite. Highly recommend to any company who is looking for a high quality e-learning and customer service (they have both in high standards).
We started using Skillcast for our employee's compliance training a few months ago and the experience has been excellent. Skillcast was very efficient in the set up process they then helped support us with rolling out our staff training in a seamless way. The course content is highly detailed and professionally delivered. Overall, I would highly recommend Skillcast as your LMS training provider.
Excellent courses with a brilliant support team
We've been using Skillcast for approx. 1.5 years and have been very happy with the service received and the courses offered. The customer service from the support team is excellent, they always respond quickly and are very helpful. The courses offered cover a broad range and the FCA courses were particularly useful to our business.
Incredibly helpful support team, who work with you to provide tailored advice and practical assistance. You are supported every step of the way. Would highly recommend.
I cannot overstate how happy with are with Skillcast. They are prompt, attentive, patient and always so good humoured. The teams work seamlessly, and there is always someone to cover in the absence of a team member. I am always impressed and very happy to work with the team.
A great LMS with a dedicated and knowledgeable team behind it. The LMS has a number of features that are gradually shared and which keeps on being developed.
Every member of the team I have had dealings with have been quick, efficient and very accommodating. No task or query is to big for them, and always a quick and prompt response. Pleasure to work with
We use Skillcast for our corporate training and it's a good LMS platform with a great variety of courses available. The platform is user-friendly and easy to navigate, and courses are up to date with legislation.
Skillcast is easy to set up and use. You can design the colours of the platform to fit you company branding. Support team are very helpful and nothing is too much trouble.
Excellent systems, user-friendly and easy to use.
Skillcast is a great platform to use for Compliance e-learning. The staff found the courses informative and engaging. There is a wide range of compliance related topics on the essentials library. The LMS is easy to use, and provides reports to track staff progress, which is a helpful feature.
The range of course libraries are comprehensive and the ability to select from multiple modules was important to us. The Global Library provides courses in multiple languages. We were also impressed with the microlearning modules. The platform is a great option for us and for our business requirements. We can also trust in Skillcast to review and update the modules so that they remain relevant and incorporate the latest developments in regulation.
Excellent services provided by the Skillcast team and the Skillcast system is simple to use.
The service provided for our company is excellent. The platform provides essential training for our business. When liaising with Skillcast in preparation for training delivery their customer service is excellent and we would definitely recommend.
Skillcast has truly transformed our approach to compliance training and tracking at Imagination. Not only does it seamlessly manage our global company's compliance requirements, but it also enhances employee engagement through its user-friendly interface and interactive content. What sets Skillcast apart is not just the platform itself, but also their exceptional customer service team. They are responsive, knowledgeable, and dedicated to providing tailored solutions to our unique needs. It's been instrumental in streamlining our compliance processes and fostering a culture of proactive risk management, growth & development."
They listened to our needs and helped tailor the existing course to our organisation with ease, ensuring accessibility requirements were maintained and the training was engaging and presentable. All their help was been very appreciated and I couldn't have asked them to do any more for us. I would recommend Skillcast to anyone looking to bring in new training modules to their organisation.
Skillcast provide an A-star product with excellent customer service support.
Feefo Customer Rating ★★★★★ 4.9/5
Ready to try this course?
Start your free trial of this course and get instant access today.
Want to explore more courses?
Browse all courses and search by topic to find what matters most to you.
Spot a Phishing Attempt
Phishing emails are fraudulent attempts by cybercriminals to trick individuals into revealing sensitive information.

Business Email Compromise
Business Email Compromise (BEC) is a targeted cyberattack where criminals impersonate executives or hack accounts to steal money or sensitive information.
Deepfake Awareness
Deepfakes use artificial intelligence to create fake images, audio or videos that can deceive individuals and organisations.

Understanding Information Security
Information security is essential to protect sensitive business and customer data from unauthorised access, breaches and cyber threats.

Common Cyber Threats
Cyber threats such as phishing, malware, ransomware and unsecured networks pose significant risks to businesses.

Zero Trust Cybersecurity
The zero trust cybersecurity model ensures IT systems remain inaccessible by default, requiring strict verification before granting access.

Bring Your Own Device Security
Bring Your Own Device (BYOD) policies offer convenience and flexibility but also introduce cybersecurity risks.

Device Hygiene
Device hygiene is the practice of keeping digital devices secure and free from cyber threats to protect company data and networks.
Malware
Malware is malicious software designed to harm or exploit computer systems, ranging from viruses and ransomware to spyware and botnets.

Ransomware
Ransomware is a type of malware that encrypts files and demands payment for their release, often causing severe financial and operational damage.
Smishing
Smishing is a targeted phishing scam that uses deceptive text messages to gain sensitive information.

Spear Phishing
Spear phishing targets specific individuals with convincing emails designed to deceive them.

Video Conferencing
Video conferencing is a vital business tool, but it also presents security and privacy risks if not used correctly.

Vishing
Vishing is a social engineering attack where cybercriminals use phone calls to trick individuals into revealing sensitive information.
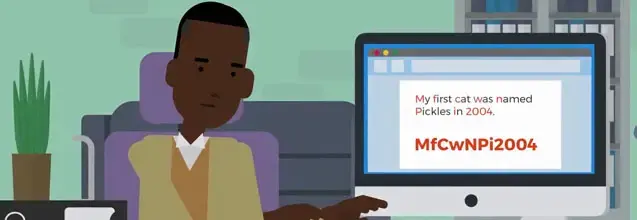
Creating Strong Passwords
Strong password protection is essential to safeguarding company systems from cyber threats such as brute force attacks and password guessing.
Multi-factor Authentication
Multi-factor authentication (MFA) enhances security by requiring users to verify their identity through multiple authentication methods.

Reacting to Password Breaches
Password breaches can lead to unauthorised access, fraud and data theft, often resulting from weak passwords, phishing or insecure networks.

Information Classification
This training helps employees understand different levels of information classification, their restrictions and how to handle data securely.
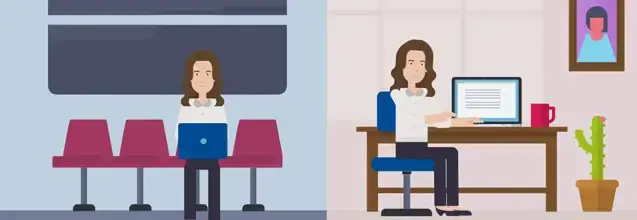
Information Security on the Move
Handling company information securely, especially when working remotely or traveling, is essential to prevent data breaches and security risks.

Tailgating and Piggybacking
Cybersecurity is not just about digital protection but also involves securing physical access to critical systems.

Secure Web Browsing
Practicing safe web browsing helps to reduce security risks and protect sensitive information.
Supply Chain Cybersecurity
A company’s cybersecurity is only as strong as its weakest link and supply chain vulnerabilities can expose businesses to major breaches.

Transferring Information Securely
Securely transferring information is essential to protect sensitive data from breaches, legal risks and business disruptions.
Using Wi-Fi safely
Wi-Fi connectivity offers convenience but also exposes devices and data to security risks if not properly managed.

Advising Customers on Cybersecurity
Cybersecurity is everyone's responsibility, including guiding customers to protect themselves from online threats.

CEO Fraud
CEO fraud is a type of Business Email Compromise where cybercriminals impersonate executives to trick employees into making payments or sharing confidential information.

Guide to Secure Remote Working
Remote work provides flexibility but also introduces cybersecurity risks that can compromise company data and systems.
Think Before You Click
Clicking on malicious links or attachments is one of the most common ways cybercriminals infect IT systems with malware.
Our LMS or yours?
Award-winning LMS
Leverage the award-winning Skillcast Portal to deliver your compliance training, track performance with analytics, and access compliance tools to support and strengthen your compliance programme.
Skillcast Remote Services
If you prefer to use your own LMS, we offer flexible pricing plans and delivery options to suit your unique needs, from off-the-shelf course libraries to fully bespoke solutions.
.png?width=1500&name=Ask%20Aida.%20Get%20Answers.%20(1280%20x%20720%20px).png)
Bring your courses to life with AI
Boost staff engagement by putting support and just-in-time learning front and centre. Aida delivers instant, reliable answers to compliance questions and recommends policies or training directly within your daily workflow, including MS Teams and soon Copilot. This reduces repetitive queries for your compliance team and helps identify knowledge gaps and risks.
Your questions, answered
DORA
Common FAQs
How can I benchmark my team's cyber security awareness?
Are Skillcast courses SCORM-compliant?
What other tools are needed beyond training?
Is our training content still compliant with the latest legislation?
- You can check the latest course content updates in our library updates page: https://www.skillcast.com/compliance-course-library-updates
- For major legislative changes, we:
- Send you email alerts to ensure you are notified
- Offer you a free trial of newly created or updated content
- Host webinars with compliance experts to explain the changes and how our training supports your ongoing compliance
Can you translate our content into other languages?
What file types are supported by the Skillcast system?
Features |
Supported file types and details |
|
File Exchange |
File types: PDF, Excel spreadsheets, Word documents, SCORM and xAPI files, and compressed zip files. Max file size: Default is 1GB, can be increased to a max of 2GB |
|
SCORM files |
Versions: SCORM 1.2, SCORM 1.2 for Moodle, SCORM 2004 2nd, 3rd and 4th Edition. Max file size: 1024MB |
|
xAPI file |
Max file size: 2GB |
|
Videos |
File types: MP4 or MOV. Videos must be optimised, with a max file size of 100MB. If the file is bigger, our Design Team can help |
|
Images |
File types: jpg, png and gif. The file size should ideally be 100KB, but it can be up to 250KB |
|
CPD evidence |
File types: Word, PDF, Excel and CSV. File size: the limit should be whatever the portal config option is set to. Servers are set to max 2GB |
|
Policy documents |
PDF or Word File size: the limit should be whatever the portal config option is set to. Servers are set to max 2GB |
|
Offline activities evidence |
File types: PDF, DOC, DOCX, XLS, XLSX, CSV, PNG, GIF, JPEG, JPG, PPTX and MSG. File size: the limit should be whatever the portal config option is set to. Servers are set to max 2GB |
|
Client logo files |
File types provided by client: EPS, PDF, AI and SVG |
|
Registers |
PDF, DOC, DOCX, XLS, XLSX, CSV, PPT, PPTX, POT, PPA, PPS, JPG, JPEG, PJEPG, PNG, BMP, GIF, MP4, MOV, WMV, CPTX, CP, TXT, ZIP and MSG files |
|
Declarations |
JPG, JPEG, PNG, GIF, XLS and XLSX files |




-ID.webp?)








_ID.webp?)